Can someone suggest the best practices for mitigating against DoS attacks?
So far it looks like Cloudflare seems to the be the standard approach in the community.
Cloudflare does a pretty decent job but there are many cases where it doesn't help and others when it even complicates the situation by masking the offending IP.
what I recommend, based on the experience we had at the Olympics site, is to use a combination of hardening the OS and nginx with iptables and fail2ban:
- https://www.cyberciti.biz/tips/linux-unix-bsd-nginx-webserver-security.html
- https://www.nginx.com/blog/mitigating-ddos-attacks-with-nginx-and-nginx-plus/
- https://easyengine.io/tutorials/nginx/fail2ban/
I can share a basic fail2ban configuration with you.
Thanks @hvelarde.... so you actually don't use Cloudflare?
yes, we use Cloudflare but there are some sites where we can't use it because we don't control the DNS.
Could you share it on the ansible playbook? I seem to recall that there is a fail2ban ther, or someone asked to be added there.
the fail2ban configuration is tightly related to the nginx configuration; I prefer to share it on a blog post.
let me see if I can find time for that tomorrow.
Keep in mind that cloudflare is only one example of CDNs and there are others out there which have better reputation for DDoS protection. You are paying for their insight and monitoring of the incoming traffic as well as just having big fat pipes and lots of servers to handle extra load.
Also using a CDN to DDoS requires you keep your server secret.
fail2ban seems enabled in the playbook... at least it is on in plone.io
Paid CF plans do not have this problem ![]()
But even if you don't want to pay for CF, you may not care what the real originating IP is, and so the free CF plans are amazingly good.
Yes, CF is the standard ("not Hector") approach ![]() It is also what we use for many Plone Foundation sites.
It is also what we use for many Plone Foundation sites.
You're talking about the Cloudflare Pro or Business level? One issue I've had with early tinkering is related to clearing the cloudflare cache.
It's possible there is something out there that clears CF cache from Plone. I'm pretty sure Castle has that. Or I think you can do it from CF's interface. But what we often do is maintain a public heavily cached URL and a different less heavily cached URL for content editing.
Makes sense... I've done that whole public vs content editing interface approach before. As long as the project I'm working on is okay with maybe 1 hour buffer the content goes live I suppose that could work. Worst case I'd go into CF and purge stuff.
I figure there must be a way to automate this with the CF api, or integrate a control panel in Plone.
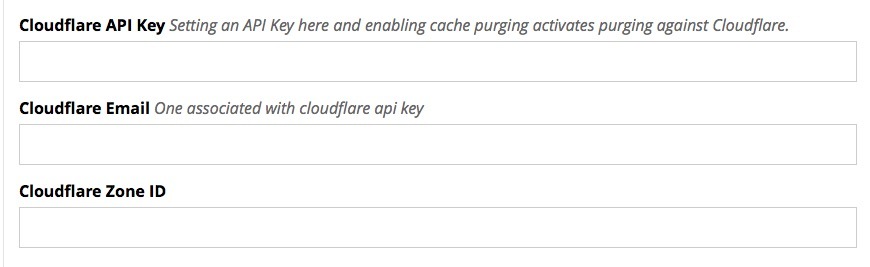
This is part of the Castle control panel where you enter various keys to enable optional functionality.
The code that uses it is at https://github.com/castlecms/castle.cms/blob/cb8296e7a1c3daf0be46341a6e779868b6d34694/castle/cms/caching/cloudflare.py#L40
Nice! Must keep this on my radar.
Keep in mind that if you have one URL for the public and other URL that goes direct you have negated any ddos protection.
I use cloudflare but something I dont like (other than non standard purging) is it doesnt obey a lot of the standard caching headers. You can't use it to cache html pages for example for a few min. A very handy trick if your site is high volume.
Cloudfront does this. If you are on aws anyway its pretty cheap.
you're wrong on this: DDoS these days are really hard to block if you don't know the real IP of the attacker: its pretty easy to skip Cloudflare basic protection generating a lot of useless requests that are going to bypass all your caching and block your instances in a couple of minutes.